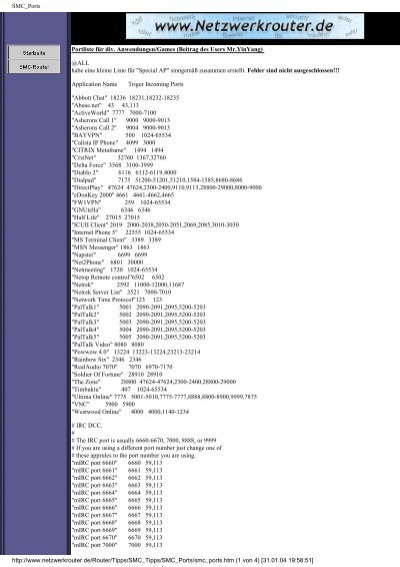
List of well-known ports used by various peer-to-peer (P2P) protocols. | Download Scientific Diagram
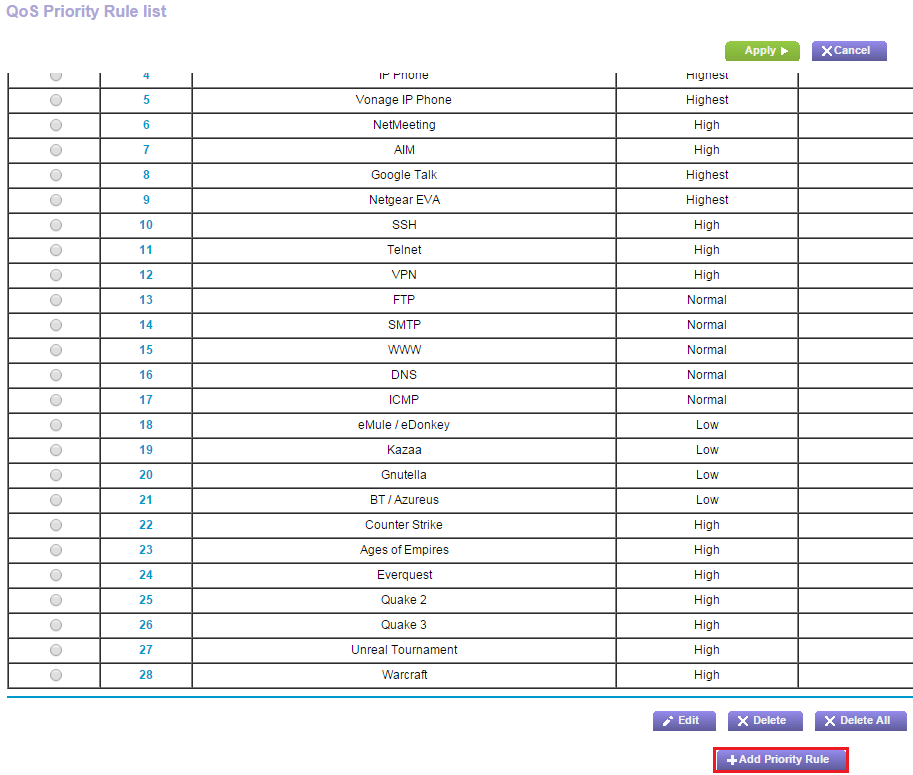
How do I set up a QoS policy for a device that is connected to a LAN port on my Nighthawk router? | Answer | NETGEAR Support

PDF) A Peer-To-Peer Traffic Identification Method Using Machine Learning | Feng Wenfeng - Academia.edu

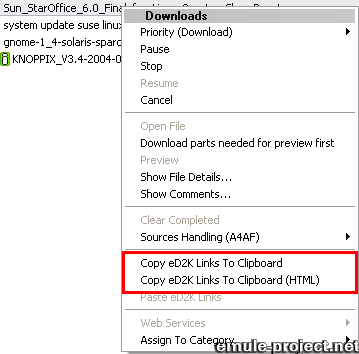
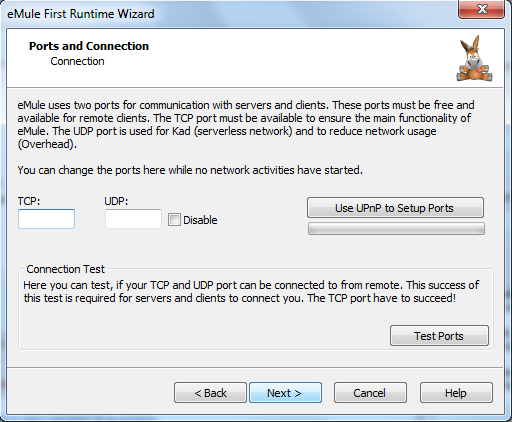
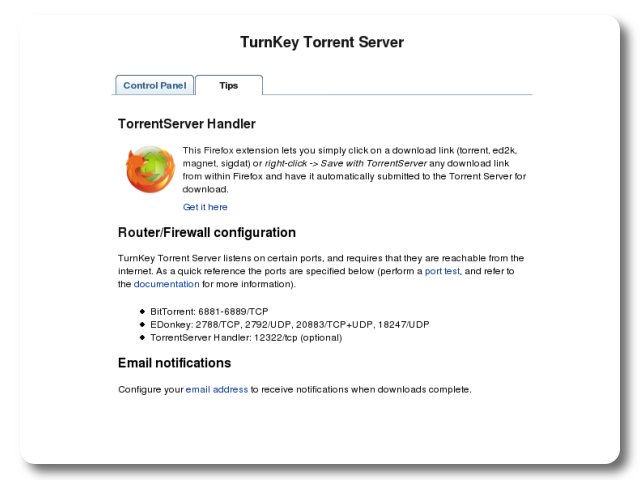
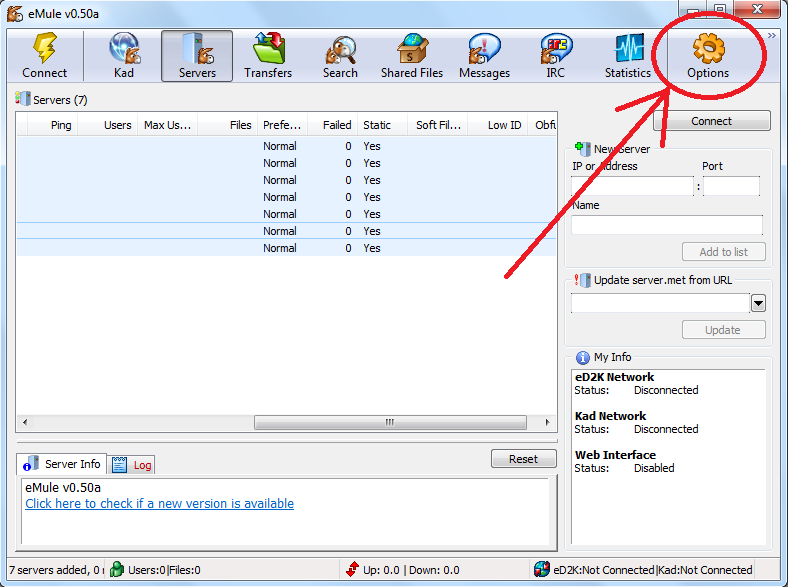
![using_emule_plugin [BitComet Wiki] using_emule_plugin [BitComet Wiki]](http://wiki.bitcomet.com/_media/em_05.png)


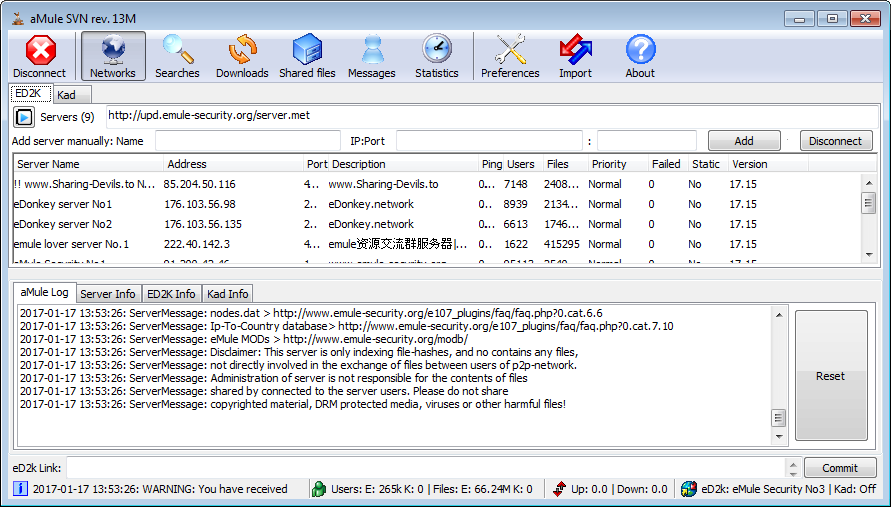
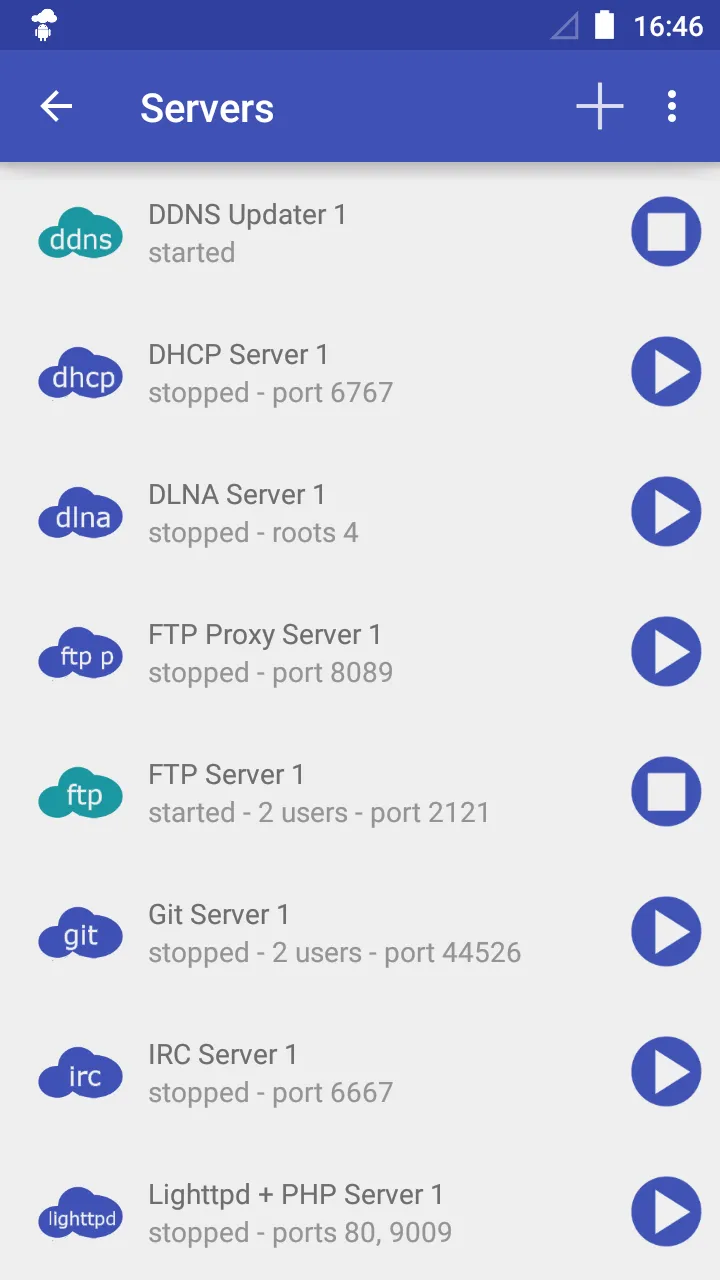
![using_emule_plugin [BitComet Wiki] using_emule_plugin [BitComet Wiki]](http://wiki.bitcomet.com/_media/em_09a.jpg)

![PDF] A Survey: Peer-to-Peer Traffic Identification technologies | Semantic Scholar PDF] A Survey: Peer-to-Peer Traffic Identification technologies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ae8296f5217ce9eb8c90751fd9421ca2cc8484ca/2-TableI-1.png)